Smartphones have fundamentally transformed modern communication and work habits, becoming indispensable tools for millions globally. As these devices are increasingly used for sensitive transactions—ranging from online banking to accessing governmental services—the imperative for robust security becomes ever more critical. However, a significant analysis conducted by researchers at Graz University of Technology (TU Graz) has raised serious concerns about the vulnerabilities present in the Android kernels used by leading smartphone manufacturers. This article will dissect the findings of the study, offering critical insights into the implications for both consumers and manufacturers.
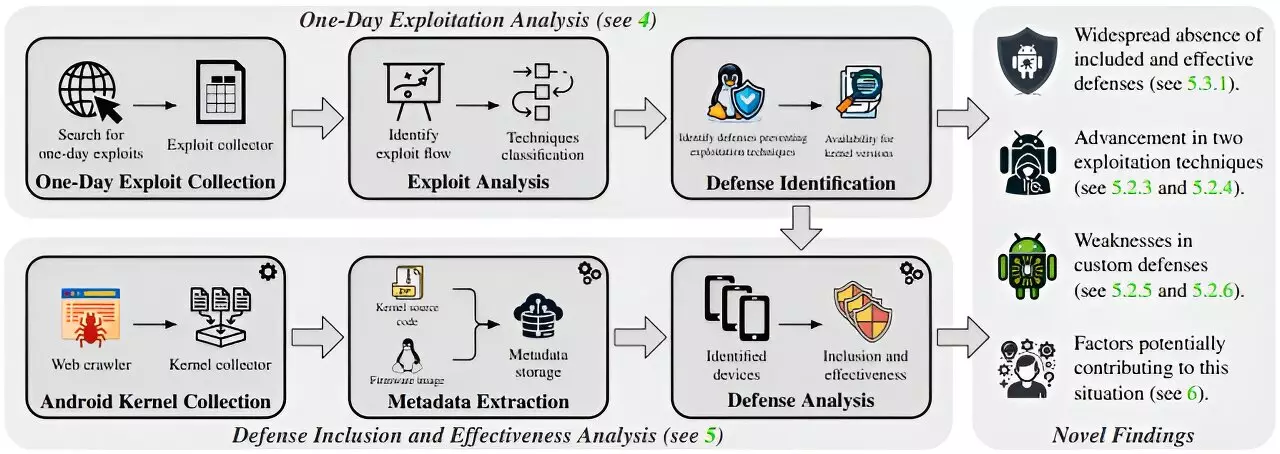
The study analyzed the Android kernels from ten prominent smartphone manufacturers, examining a total of 994 devices released between 2018 and 2023. Researchers Lukas Maar, Florian Draschbacher, Lukas Lamster, and Stefan Mangard revealed startling statistics: between 29% and 55% of the devices tested were able to thwart known one-day exploits—attacks that utilize publicly acknowledged vulnerabilities. In stark contrast, Google’s Generic Kernel Image (GKI) version 6.1 was found to offer a significantly higher level of protection, effectively defending against approximately 85% of potential attacks. This discrepancy raises questions about the relative performance of manufacturer-specific kernels, which proved to be up to 4.6 times less effective in safeguarding against malware.
One of the critical observations from the TU Graz analysis was that many known security methods, which could effectively counteract existing attack techniques, were either insufficiently activated in the manufacturers’ kernels or configured incorrectly. Surprisingly, even older kernel versions, such as 3.10 from 2014—if configured correctly—could outmatch nearly 38% of modern kernels in preventive capabilities. This revelation highlights a fundamental flaw not just in device security but also in the manufacturers’ approach to prioritizing efficiency over robust security measures.
The analysis further unveiled a worrying trend: low-end smartphone models were approximately 24% more vulnerable to attacks compared to their high-end counterparts. This vulnerability arises from the deliberate deactivation of additional security measures on less powerful devices to conserve processing resources. This trade-off between performance and security exposes a critical dilemma that manufacturers face. As demand for budget-friendly devices continues to rise, security considerations often take a back seat, potentially endangering consumers who may not be aware of the inherent risks.
In light of these findings, the urgency for addressing these vulnerabilities cannot be overstated. The researchers have initiated dialogues with key industry players, including Google, Fairphone, Motorola, Huawei, and Samsung. Notably, some manufacturers have already acted on the reported vulnerabilities, releasing patches aimed at improving kernel defenses. The researchers also suggested that Google revamp its Android Compatibility Definition Document (CDD) to incorporate more stringent requirements for kernel security, thereby motivating manufacturers to adopt better practices.
As smartphones continue to evolve as central tools for both personal and professional use, enhancing their security remains paramount. The TU Graz study lays bare an unsettling vulnerability landscape, underscoring that many manufacturers have room for improvement in their kernel security measures. Moving forward, efficiency should not eclipse the necessity for robust security frameworks. If the industry can operationalize these insights, it could pave the way for a safer digital experience for consumers worldwide. As emphasized by researcher Lukas Maar, reinforcing these security measures is not merely an option but a responsibility that manufacturers must embrace to ensure a secure future in the age of pervasive technology.
The findings from TU Graz serve as a wake-up call. Both manufacturers and consumers must recognize that the stakes are high; security vulnerabilities in smartphones extend beyond individual users to affect entire ecosystems. Therefore, a collective response from the industry will be essential in fortifying defenses against future threats.
Leave a Reply